





























One of the interesting and challenging aspects of working in the Mobility space is the sheer pace at which the industry is moving. I'm fortunate to work with many Customers in EMEA to help support and shape their strategy towards Mobile technology. A great example of this has been the reaction to BYOD.
The influx of personal devices into the Enterprise caused by the BYOD trend poses numerous challenges to IT Departments. Understandably, initial reaction was to focus on network and device level Security.
Cisco responded by introducing a BYOD Solution to remove some of the burden from IT Departments and provide them with a central point for managing many aspects of the BYOD lifecycle: onboarding, device profiling, authentication, authorization, offboarding and self-service management.
Almost at the same time, a new industry segment was created: Mobile Device Management. The intent of MDM systems isto provide device oriented security management: PIN lock enforcement, encryption, jailbreak detection, geofencing etc.
The opportunities in BYOD caused a rapid rise in the number of MDM vendors and associated solutions. In fact, there is now estimated to be over one hundred Enterprise level offerings and the market is widely accepted to be saturated. We expect to see much in the way of consolidation in 2014.
Cisco recognizes the need for both solutions to coexist and in the latest release provides a first phase integration to some of the leading MDM systems. An example of the benefit of this integration is a simplified enrollment process: Cisco BYOD will check and enforce registration with an associated MDM (Figure 1 below).
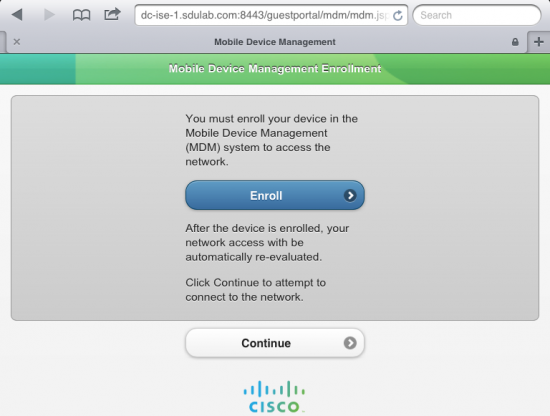 Figure 1: ISE integration with Mobile Device Management
Figure 1: ISE integration with Mobile Device ManagementBut things move fast when it comes to Mobility! I have noticed many of our Customers starting to focus beyond belts and braces security. They are now looking at the benefits that could be accrued from having a more expansive Mobility strategy.
And this has turned attention to what aids and improves productivity on Mobile Devices: applications and data.
CIOs and CTOs know this is the combination that fuels productivity and supports new business models. But at the same time, Apps and Data need to be carefully managed from a security perspective. Thus the terms Mobile Application Management (MAM) and Mobile Content Management (MCM) have been coined. Indeed the industry seems to have settled on the term Enterprise Mobility Management (EMM) to capture all three components: MDM, MAM, MCM.
For example, in BYO scenarios, Apps typically come from public App stores (Figure 2). But which Apps are allowed to interact with company resources? Are these Apps allowed to transfer and store company data on personal devices? What happens if a device gets lost or stolen, or an employee leaves the Company?
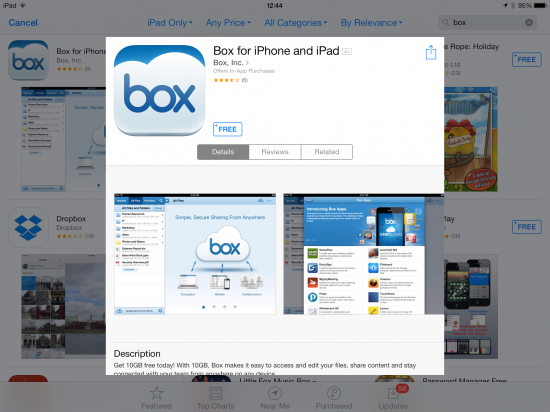 Figure 2: Example of a public App often used for business purposes
Figure 2: Example of a public App often used for business purposesIt is clear that solutions to MAM and MCM must integrate with network security. Compromised devices may need to be kept off the corporate network or access privileges restricted. Ideally, policies for MAM and MCM would be centralized to minimize IT Admin overhead and support all modes of access, device types, application formats and data repositories.
Look out for future Blogs on this subject where we will explore how the Cisco BYOD solution is evolving to support EMM. For now, check out www.cisco.com/go/mobility for more on Cisco Mobility solutions.
 Hot Tags :
Business
#Security
BYOD
Mobile Device Management
Enterprise
device
mobile device
authentication
IT department
Hot Tags :
Business
#Security
BYOD
Mobile Device Management
Enterprise
device
mobile device
authentication
IT department