





























This post was authored by Rich Johnson, William Largent, and Ryan Pentney. Earl Carter contributed to this post.
Cisco Talos, in conjunction with Apple's security advisory issued on June 30th, is disclosing the discovery of a remote code execution vulnerability within Apple Quicktime. This vulnerability was initially discovered by the Talos Vulnerability Research & Development Team and reported in accordance with responsible disclosure policies to Apple.
There is a remote code execution vulnerability in Apple Quicktime (TALOS-2015-0018/CVE-2015-3667). An attacker who can control the data inside an stbl atom in a .MOV file can cause an undersized allocation which can lead to an out-of-bounds read. An attacker can use this to create a use-after-free scenario that could lead to remote code execution.
There is a function within QuickTime (QuickTimeMPEG4!0x147f0) which is responsible for processing the data in an hdlr atom. There is a 16-byte memory region, allocated near the beginning of the function, if the hdlr subtype field in an mdia atom is set to 'vide', this reference is passed to a set of two functions.

The first function swaps out the reference in object_ref for a bigger object, one of size 0xb0 bytes, and the second function operates on this new object.

At some point up the call stack, for the first of these two functions, the reference in question is passed to the functionQuickTime!0x73e0f0. However, when the stbl atom is missing from the file, or the 4CC is corrupted, the object at eax does not get populated. When this happens the check at line 15 will pass and an error code (0xfffff809) will be passed back down the call stack.
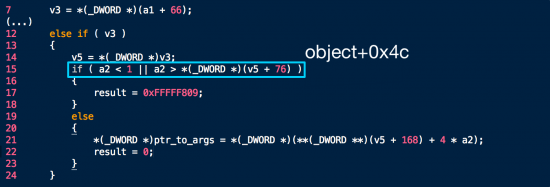
This series of calls would normally lead to the replacement of the object reference lie in the functionQuickTime!0x748a40.However, because the error code returned down the stack isn't zero, the branch below is taken and the code path skipped.

Eventually, the calls return and the function at line 57 ofQuickTimeMPEG4!0x147f0is called.

Code execution makes its way up to the functionQuickTime!0x21ab00.

A read of 2 bytes is attempted at an offset of 84 bytes into the 16-byte object, resulting in an out-of-bounds read.
Cisco Talos' research and discovery of programmatic ways to find 0-days helps secure the platforms and software that our customers depend on. The disclosure of this and other vulnerabilities helps the entire online community by identifying security issues that otherwise could be exploited by threat actors. Uncovering new 0-days not only helps improve the overall security of the software that our customers use, but it also enables us to directly improve the procedures in our own security development lifecycle, which improves the security of all of the products that Cisco produces.
Related Snort rules: 35022-35023
For the most up to date list, please refer to Defense Center or FireSIGHT Management Center.
For further zero day or vulnerability reports and information visit:
http://talosintel.com/vulnerability-reports/
Timeline ::
2015-05-08 -Reported
2015-06-30 -Patched
2015-06-30 -Released
 Hot Tags :
Apple
#Security
Cisco Talos
Talos
vulnerability
0-day
vulnerability spotlight
research
stbl
Hot Tags :
Apple
#Security
Cisco Talos
Talos
vulnerability
0-day
vulnerability spotlight
research
stbl