






























I'll admit to not having done a thorough verification. However, I'd still bet money that AAA/RBAC services are more frequently mentioned on Cisco certification blueprints than any other networking topic. From the CCNA to the Expert level, you'll find AAA, TACACS+, RADIUS, and RBAC listed on the exam topics.
Here is a handful of examples if you'd like to check it out yourself:
OMG.That's 10 different certifications from Associate to Professional where these topics show up. You'll also find them on Expert-level exams, such as the Enterprise Infrastructure, Enterprise Wireless, Security, Service Provider, and Data Center labs. (If anyone out there can find another topic with as broad a coverage, please let me know in the comments. I'd love to know what I've overlooked so far.)
AAA is an important topic, but it's one that even long-time network engineers may not fully understand. So before we see it in action, how about a quick overview of what the "triple A's" mean?
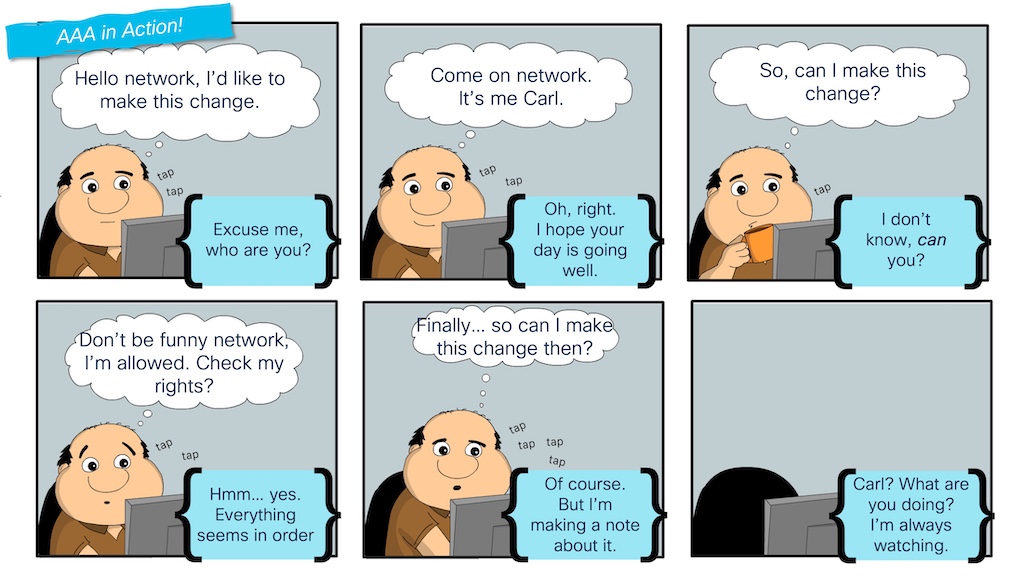 Carl sees how Authentication, Authorization, andAccounting are separate and important steps for device administration.
Carl sees how Authentication, Authorization, andAccounting are separate and important steps for device administration.In the "AAA in Action!" comic, Carl experiences the entire AAA process:
TACACS comes into the picture to support the centralized management of users, roles, and logs (authentication, authorization, and accounting). While each network device could be locally configured to handle AAA, this doesn't scale well for enterprises. A better solution is for each network device to communicate with a central "server" for these actions. TACACS is a protocol that network devices and servers use to communicate and handle each of the "A's." A "TACACS Server" is a software application that supports the TACACS protocol.
Now that we understand the critical role that AAA plays in a network (and that it is an essential topic across many certifications), I'd like to show you how to study and prepare for it using my favorite network simulation/virtualization tool: Cisco Modeling Labs (CML). Because I'm all about sharing my exploration activities, I posted a couple of CML topology files on GitHub in the CML-community repository under Cisco DevNet.
You'll see that one CML topology includes just an IOL router, while another adds a Nexus 9000v switch to cover data center platforms as well. So, after you've read this blog post, definitely download the topologies and explore them yourself.

Before you can configure TACACS on a switch or router, you must have a TACACS server available in the network. A common TACACS server for a production network is Cisco ISE, a full "identity services engine" for device administration, network access, wireless security, VPN access, and more.
Cisco ISE is an important product and topic for network engineers. In fact, we have a certification exam dedicated to it. And while you can add Cisco ISE to a CML node library using the node definition available at the CML-Community, running a full ISE server in the topology can feel overkill when the focus is just on configuring TACACS for device administration.
Thankfully, there are lightweight alternatives. My go-to option is the open-source "tac_plus" application that has been available for many years. Tac_plus is a basic Linux application that can be downloaded and installed on most Linux distributions. While active development of the project seems to have stalled, it works great and continues to be an excellent option for cases such as this.
If you look at the image of the CML topology, you'll see "aaa-server" on the left-hand side of the diagram. This is a standard Ubuntu node from the CML reference platforms, with a starting configuration setup to install tac_plus and configure it as a basic TACACS server. Feel free to go and check out the configuration in the topology file for full details, but here are the basics of what I did to build my TACACS server:
With the installation and configuration of the aaa-server part of the base CML topology file, tac_plus will be running and ready to take requests as soon as the lab is started.
cisco@aaa-server:~$systemctl status tac_plus
 Hot Tags :
Network security
Cisco Certifications
AAA
CML
Hot Tags :
Network security
Cisco Certifications
AAA
CML