




























Classifying and compartmentalizing information has been around within the Department of Defense before it was even called the Department of Defense. However, as DOD information that was once secured in vaults and safes has become digital data, many new regulations have been introduced that mandate how this data should be processed and handled. These regulations address the classification of the data, but they also address the segmentation of data and users.
Over the past few decade, as DOD data has moved to digital formats stored in data centers across the network, the same regulations that were used to govern the data classification and compartmentalization have also been applied to the network. And as networks have become increasingly complex over the past ten years, new requirements have been released that not only dictate data classification and compartmentalization, but also how different types of networks within the same classification are to be segmented from each other. These requirements also apply tighter controls on enclaves within the organizations' larger network, segmenting the network even more.
Despite the new regulations, network segmentation is nothing new to DOD. Traditionally, DOD network segmentations were accomplished with access control list (ACL) on an enclave firewall or router. However, today's networks are much more complex than the networks were just ten years ago. The DOD has responded to the increased complexity with more and more requirements, making it more and more difficult for edge devices such as firewalls and routers to be the lone enforcement device for network segmentation. As complexity and requirements increase, manageability decreases. This makes DOD network segmentation a daunting task for any network and cyber administrator.
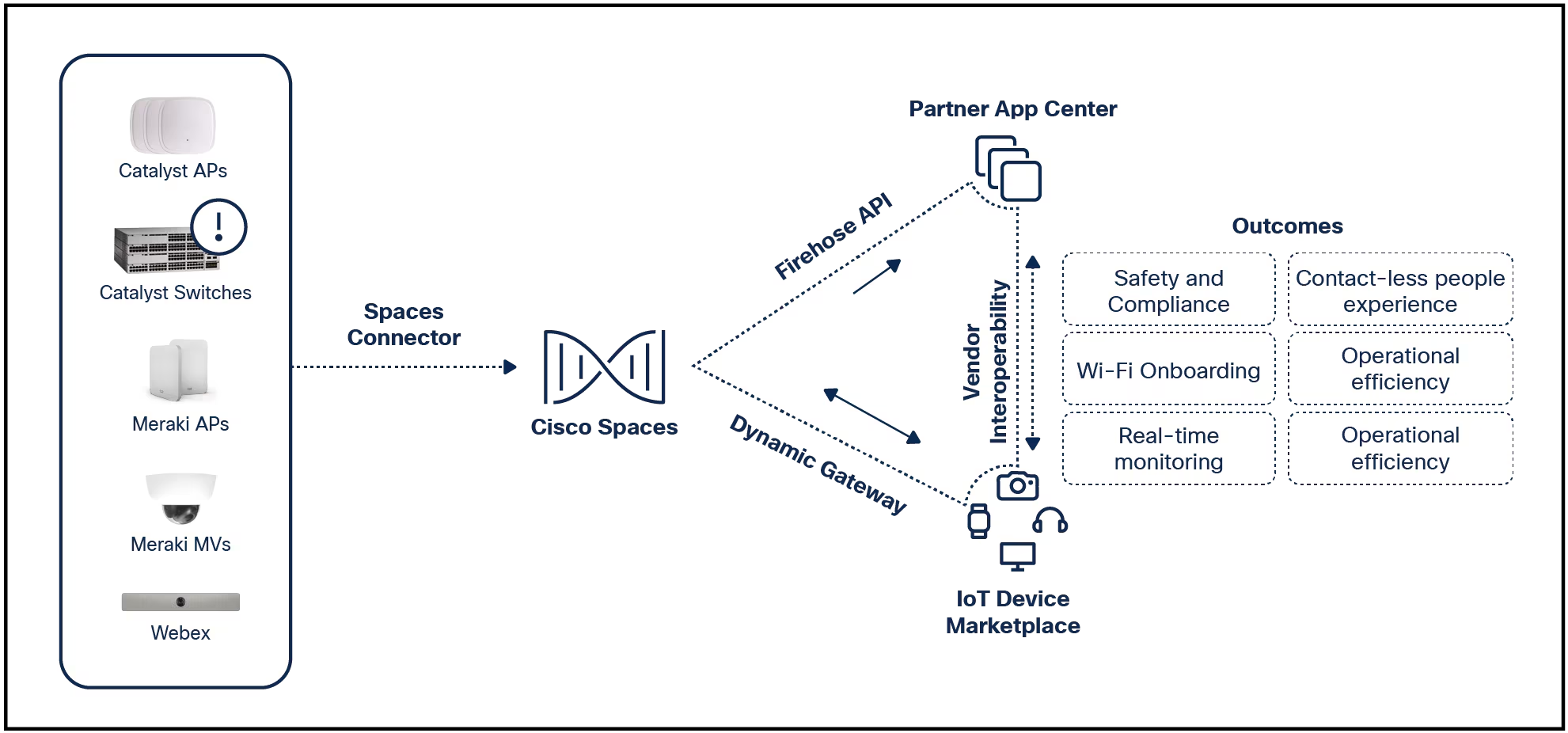
But network segmentation is nothing new to Cisco either. Our cybersecurity solutions make network segmentation easily manageable, despite the complexity. Cisco's Identity Services Engine (ISE), along with Cisco TrustSec and StealthWatch, build network segmentation directly into the network itself. Our technology uses policy-driven segmentation based on identity to simplify the provisioning of network access, accelerate security operations, and provide consistent enforcement anywhere in the network. Best of all, Cisco TrustSec is embedded technology in Cisco switches, routers, wireless controllers and security devices. It's what we mean by "Network as an Enforcer": the network itself can enforce segmentation policy, all from a centralized console that makes the policy easy to manage. And in the face of today's challenge of recruiting and retaining cybersecurity professionals, effective management becomes an absolute must.
We know how important it for DOD agencies to keep their data safe, and we also understand that the more manageable a security solution is, the better it work. It's why we enabled Cisco's networks to become the effective enforcer, and why we're laser-focused on making everything simpler and easier to manage. To learn more about how Cisco is helping the DOD with network segmentation, check out our Cyber Threat Defense here.
 Hot Tags :
Cybersecurity
Cisco Identity Services Engine (ISE)
Cisco Stealthwatch
Cyberattacks
Department of Defense (DoD)
TrustSec
Network Segmentation
defense
information security
Hot Tags :
Cybersecurity
Cisco Identity Services Engine (ISE)
Cisco Stealthwatch
Cyberattacks
Department of Defense (DoD)
TrustSec
Network Segmentation
defense
information security