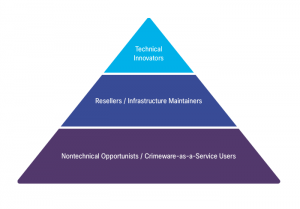
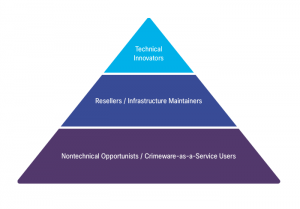
We know that as time goes on, the cybercrime network's operations will only more closely resemble those of any legitimate, sophisticated business network. And like all enterprising businesspeople, those who are part of the "cybercriminal hierarchy"-which is discussed in theCisco 2014 Annual Security Reportand illustrated below-look to increase their profits by continually innovating new products and improving upon existing ones.
This was certainly the trend in 2013: Cisco researchers observed cybercriminals applying several tried-and-true techniques in new, bold, and highly strategic ways. TheCisco 2014 Annual Security Reportexamines some of these actions and our associated research in detail, including:
- Brute-force login attempts:There was a threefold increase in the use of brute-force login attempts just in the first half of 2013. Cisco TRAC/SIO researchers discovered a hub of data with millions of username and password combinations that malicious actors were using to feed these actions. Many brute-force login attempts are being directed specifically at popular content-management system (CMS) platforms like WordPress, Joomla, and Drupal. (Read theCisco 2014 Annual Security Reportto find out why CMS platforms are favored targets-especially for adversaries trying to commandeer hosting servers in an effort to compromise the Internet's infrastructure.)
- Distributed denial of service (DDoS) attacks:Another oldie but goodie among cybercrime techniques, DDoS attacks have been increasing in both volume and severity since 2012. But today's DDoS attacks aren't just about creating disruption for businesses or making a political statement. There is evidence some attacks are now being used as smokescreens to conceal the theft of funds. TheDarkSeoul attacks, examined in theCisco 2014 Annual Security Reportand a big focus for our researchers last year, are an example of this strategy. Looking ahead, we expect DDoS attacks launched through DNS amplification to be an ongoing concern. (It's not a big leap when you consider The Open Resolver Project reports that 28 million open resolvers on the Internet pose a "significant threat.")
- Ransomware:In 2013, we saw many attackers moving away from traditional botnet-driven infections on PCs and increasing their use of ransomware. This includes a new type of malware in this category called Cryptolocker, which our researchers discovered last fall. Ransomware prevents normal operation of infected systems until a prescribed fee is paid. It provides a direct revenue stream for attackers-and it's hard to track.
The Cisco 2014 Annual Security Reportalso notes that while the tactics used by today's profit-oriented online criminals are only growing in sophistication, there's a shortage of security talent to help organizations address these threats. The bottom line: Most organizations just don't have the people or systems to monitor their networks consistently. There's also a clear need for data scientists who can help the business understand why cybersecurity needs to be a top priority, and how security and business objectives can (and should) be aligned.






























 Hot Tags :
Security
TRAC
2014 annual security report
Annual Security Report
CASR
Hot Tags :
Security
TRAC
2014 annual security report
Annual Security Report
CASR